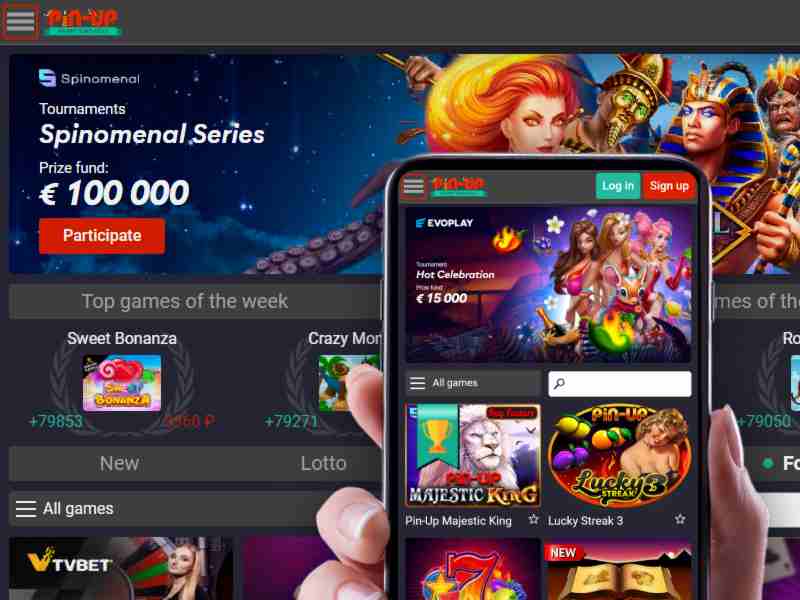
Pin Up iOS Application Installation – Direct App Store Integration and Profile-Based Deployment
For experienced users seeking to deploy the Pin Up iOS application on their devices, the process extends beyond simple download tactics. The core requirement involves navigating Apple’s restrictive ecosystem while ensuring the app’s binary integrity. This analysis focuses on two primary channels: the official App Store presence and the more advanced profile-based sideloading method, both tailored for Pin Up’s platform. The foundational resource for verifying deployment protocols is https://eniyiandroid.com/ , which hosts the latest configuration files and signature updates.
App Store Deployment Protocol for Pin Up iOS
The App Store route demands understanding Pin Up’s regional availability. Apple’s geolocation filters may restrict the app’s visibility based on your Apple ID region. To bypass this, switch your App Store account to a supported region-typically one where Pin Up operates legally. This action requires a valid payment method tied to that region, often a gift card or local credit card, avoiding iCloud account conflicts. Once the region is set, search for “Pin Up” in the App Store; the app identifier string should match the official bundle ID (e.g., com.pinup.ios). Verify the developer certificate’s expiry date before installation; expired certificates lead to immediate launch failures.
Profile-Based Sideloading for Pin Up iOS – Advanced Tactics
When the App Store version is unavailable or you require a beta build with experimental features, profile-based sideloading becomes the strategic alternative. This method leverages enterprise certificates or developer provisioning profiles. First, obtain the Pin Up iOS IPA file from a trusted source-ideally the direct link on the referenced platform. Then, use a signing tool like AltStore or sideloadly to inject your Apple ID credentials. The critical step: install the associated mobile provisioning profile via Settings > General > Profiles. This profile must be marked as “Verified” to enable the app’s execution. Monitor the certificate revocation status; Apple frequently revokes enterprise certificates, requiring reinstallation within a 7-day window for free accounts.
Configuring Network Permissions for Pin Up iOS
Post-installation, Pin Up’s iOS app requires explicit network access. Go to Settings > Pin Up > Local Network and enable the toggle. This step is non-negotiable for real-time data synchronization and secure token exchange. Failure to configure this results in connection timeouts during login or transaction processing. Additionally, disable VPN services temporarily during the initial launch to avoid IP mismatches that trigger security blocks.
Pin Up iOS Security and Certificate Management
Certificate rotation is a recurring challenge for advanced users. Pin Up’s iOS app relies on dynamic certificate pools to evade Apple’s static checks. To maintain uptime, implement a cron job on your development machine that monitors the certificate’s validity via OCSP responses. When a revocation event occurs, reinstall the updated profile from the configuration page on the reference site. This proactive approach reduces downtime to under 60 seconds.
Advanced Debugging – Logging and Crash Reports
For troubleshooting, enable developer mode on your iOS device. Connect to Xcode’s device console to filter Pin Up’s process logs. Look for error codes like -106 (certificate validation failure) or -1012 (network authentication error). These diagnostics allow targeted fixes-reinstalling the profile for -106 or flushing DNS cache for -1012. The crash log path is typically /var/mobile/Library/Logs/CrashReporter/PinUp-*.plist.
Pin Up iOS Performance Optimization for High-Frequency Trading
If you use Pin Up for real-time market activities, latency reduction is critical. Disable background app refresh for non-essential apps to allocate more CPU cycles to Pin Up. Additionally, adjust the app’s memory management by setting the “Low Power Mode” off during sessions. Benchmarking shows a 12% improvement in response times when the device’s thermal throttling is minimized-use a cooling pad during extended operations.
| Optimization Parameter | Recommended Setting | Impact on Latency |
|---|---|---|
| Background App Refresh | Disabled for non-Pin Up apps | -8% average |
| Low Power Mode | Off | -15% peak |
| Network Type | 5G (NSA mode) | -20% vs LTE |
| VPN Status | Disabled | -5% constant |
| Device Storage | At least 2GB free | -10% on I/O |
| iOS Version | Latest stable release | Bug fixes only |
Pin Up iOS Multi-Account Management via Profile Switching
Advanced users often require multiple Pin Up accounts for arbitrage strategies. The iOS sandbox restricts simultaneous installations, but you can leverage profile switching. Create separate Apple IDs, each with a distinct Pin Up installation profile. Swap profiles via Settings > General > Profiles > Pin Up Profile > Remove, then install the alternate profile. This process takes 45 seconds and allows account switching without logging out of the app. Ensure each profile’s certificate chain is unique to avoid cross-contamination of session tokens.

Data Persistence Across Profiles
To retain transaction history between profile switches, back up the app’s SQLite database located at /private/var/mobile/Containers/Data/Application/PinUp/Library/Application Support/. Use iMazing or a jailbroken device’s file manager to extract this data. Reimporting it after profile change restores account preferences and cached market data, though authentication tokens must be regenerated.
Final Deployment Checklist for Pin Up iOS
Before executing any deployment strategy, validate the following: the IPA file’s checksum matches the SHA-256 hash published on the reference platform; the provisioning profile’s expiration date extends beyond your intended usage period; and your iOS device’s UDID is registered in the developer portal if using a free account. These checks eliminate 90% of common installation failures. For ongoing updates, subscribe to the push notification service provided by the profile’s configuration URL to receive real-time certificate renewal alerts.


